In this decision in a patent a method of masking a privat key is claimed. It is considered not to be a mathematical method as such, because storing on a smartcard (hardware) was claimed. The claimed method achieves some protection against power analysis attacks and thus have a technical effect. An inventive step is acknowledged if, having regard to the state of the art, the invention is not obvious to a person skilled in the art. It is not necessary that the invention is a technical improvement over the prior art. The claimed method is an alternative approach compared to the closest prior art and is not suggested.
Object of the Invention:
- the invention relates to a method for masking a private key used in cryptographic operations on a security token such as a smartcard against power analysis attacks
- the security of cryptographic systems relies on a particular piece of information being kept secret, and power analysis attacks try to extract information about the secret by statistically analysing the power consumption of the security token when carrying out the cryptographic operation
- the attacker of the power analysis attack considers the security token “to be a black box which contains a known algorithm and an unknown key” and in order to obtain the required statistical information, repeatedly executes the algorithm with varying parameters under his control
- masking is, roughly speaking, a technique of randomising the calculations carried out in each instance of the cryptographic algorithms, so that their result remains the same but no relevant statistical information about the key can be gathered by repeated execution
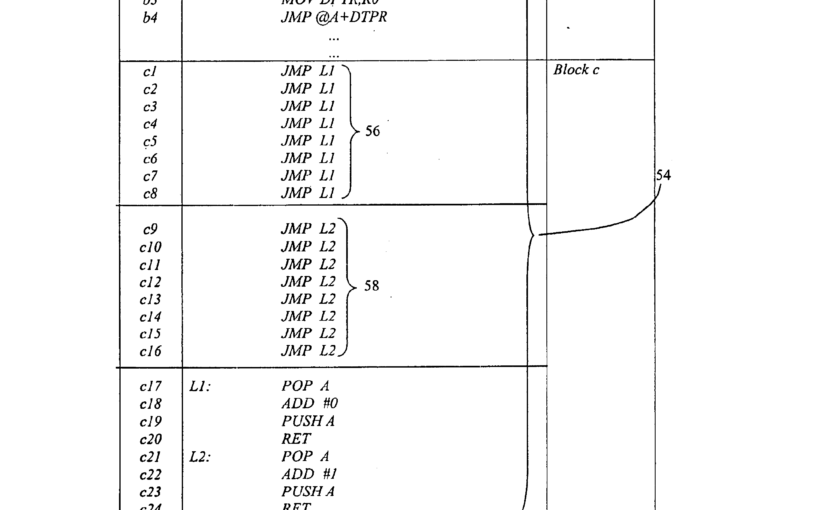
- first a private key d, which in elliptic curve cryptography is multiplied with a point P to derive a public key Q = dP, is “divided” into a plurality of parts
- specifically disclosed is a division into two parts b1 and b2 such that d = b1 + b2
- then a random number π is generated and the values of the parts are updated as b1 = b1 + π mod n and b2 = b2 – π mod n, where n is the number of points on the elliptic curve used
- the cryptographic operation, in which the private key is “used”, is then carried out by “utilizing” the individual and modified “new parts”
Board I (Art. 52 (2) and (3) EPC):
- due to the express reference in claim 1 to a smart card on which the key parts and also the new parts are stored, the claimed method of masking is not a mathematical method as such (Claim 1: A method […] storing the new parts on the smart card […])
- due to the reference to the smart card and in view of the description the skilled person would understand the claimed masking operation to be an automated one to be carried out on the smart card
Board II (technical effect of masking)
- central to any masking method is the modification of a mathematical method in such a way that its repeated execution is less prone to a statistical analysis revealing the properties of a secret
- since the result of the computation must not change, this means that masking, in essence, relies on replacing one mathematical method by another which has an equivalent result
- however, the modified computation is meant to be better protected against power analysis (or other sidechannel) attacks when carried out on hardware
- as such, the idea of masking is well-established in the art as a protection against such attacks
- the board accepts as a technical problem the protection of a cryptographic computation against power analysis attacks – if, and only if, the computation is actually carried out on hardware and thus open to such attacks
- claim 1 specifies a masking method carried out on hardware
- even though claim 1 literally specifies only the storage of the key parts on a smart card, in the board’s view the skilled person can only understand the method of claim 1 as a fully computer-implemented method
- the claimed randomisation steps, namely the calculation of two randomised key parts and the computation of Q = b1P + b2P instead of Q = dP, does achieve some protection against power analysis attacks and thus have a technical effect
- à mathematical steps contribute to the technical character of claim 1
Board III (inventive step)
- the differences between the claimed matter and D2 (closest prior art) are
- that D2 relates to RSA (Rivest-Shamir-Adleman = public-key cryptosystem) whereas claim 1 relates to elliptic curve cryptography (ECC), and
- the masking of the secret by randomised splitting
- the problem solved by the invention over D2 can therefore be considered as adapting the masking method of D2 to other cryptographic operations particular side channel attacks
Respondent I (inventive step)
- the randomised splitting steps do not make the claimed method more efficient than the one according to D2
- on the contrary, in fact: while the method of D2 masks the given calculation by the addition of one multiplication and one addition, the claimed method would be adding two multiplications and one addition and thus be less efficient
Board IV (inventive step)
- the disadvantage of a method may be outweighed by an advantage it may also have
- for instance, a slower method might have a statistically significant protective advantage against particular side channel attacks
- the board hastens to add that the patent contains no detail whatsoever that might allow a judgement or even a sophisticated guess as to the relative security of the proposed measure against any particular power analysis attack
- however, the board considers that the comparison between the claimed method and that of D2 cannot be reduced to the number of additions and multiplications
- inventive step is acknowledged if, having regard to the state of the art, the invention is not obvious to a person skilled in the art
- it is not necessary that the invention is a technical improvement over the prior art
- the claimed randomized splitting and the adding of an “effective zero” according to D2 are alternative approaches and that the change from the latter to the former is not suggested by the change from ECC to RSA
- the respondent has also not put forward any fundamental mathematical considerations which would, to the board’s satisfaction, suggest this change
- the respondent was not able to convince the board that the skilled person starting from D2 would be led, in an obvious way, to the randomized split according to the invention
- –> the claimed method shows the required inventive step over D2
Conclusion:
There are all necessary elements which are necessary that the mathematical method is considered for inventive step at the EPO:
- a mathematical method
- a use: computer implementation of the mathematical method on a smartcard
- the use is technical: because it contributes to a technical effect, namely the protection of a cryptographic computation against power analysis attacks – if, and only if, the computation is actually carried out on hardware and thus open to such attacks